Creative Red Teaming Course Mandiant
Creative Red Teaming Course Mandiant - After completing this course, learners should be able to: See this and similar jobs on glassdoor It will also show the delivery method in which the course is given. However, organizations must still follow the right processes and use proven tools to enjoy all. By applying to this position…see this and similar jobs on linkedin. Dive deep into the world of red teaming with our comprehensive review of mandiant's creative red teaming course. • identify, fingerprint and compromise a target with custom crafted payloads while bypassing antivirus (av) detection • deploy creative. This course draws on that knowledge to help learners improve their ability to prevent, detect, and respond to threats in an enterprise network. All courses can also be purchased using expertise on. This table will display a list of all courses that are available from this provider. This course draws on that knowledge to help learners improve their ability to perform advanced offensive. From syllabus to instructors, labs to learning. You will learn proven mandiant. • identify, fingerprint and compromise a target with custom crafted payloads while bypassing antivirus (av) detection • deploy creative. Basically all the classic red team topics, opsec consideration, c2 infrastructure, phishing techniques and toolings, initial acccess vectors, lateral movements, persistence techniques. After completing this course, learners should be able to: This course includes apis and techniques used to perform common malicious functionality and extends these techniques to produce reliable payloads that function across operating system. However, organizations must still follow the right processes and use proven tools to enjoy all. By applying to this position…see this and similar jobs on linkedin. Red team offensive security is an effective exercise for addressing security gaps. Red team offensive security is an effective exercise for addressing security gaps. After completing this course, learners should be able to: By applying to this position…see this and similar jobs on linkedin. This course draws on that knowledge to help learners improve their ability to prevent, detect, and respond to threats in an enterprise network. However, organizations must still follow. All courses can also be purchased using expertise on. Te u is tr ib creative red teaming o n o t d participant guide / d mandiant. Red team offensive security is an effective exercise for addressing security gaps. Basically all the classic red team topics, opsec consideration, c2 infrastructure, phishing techniques and toolings, initial acccess vectors, lateral movements, persistence. Red team offensive security is an effective exercise for addressing security gaps. This course includes apis and techniques used to perform common malicious functionality and extends these techniques to produce reliable payloads that function across operating system. Mandiant red teams have conducted hundreds of covert red team operations. It will also show the delivery method in which the course is. Te u is tr ib creative red teaming o n o t d participant guide / d mandiant. This course draws on that knowledge to help learners improve their ability to prevent, detect, and respond to. Dive deep into the world of red teaming with our comprehensive review of mandiant's creative red teaming course. From syllabus to instructors, labs to. Dive deep into the world of red teaming with our comprehensive review of mandiant's creative red teaming course. This course draws on that knowledge to help learners improve their ability to prevent, detect, and respond to. It will also show the delivery method in which the course is given. Mandiant red teams have conducted hundreds of covert red team operations.. This table will display a list of all courses that are available from this provider. All courses can also be purchased using expertise on. Dive deep into the world of red teaming with our comprehensive review of mandiant's creative red teaming course. Red team offensive security is an effective exercise for addressing security gaps. Basically all the classic red team. This course includes apis and techniques used to perform common malicious functionality and extends these techniques to produce reliable payloads that function across operating system. Te u is tr ib creative red teaming o n o t d participant guide / d mandiant. This course draws on that knowledge to help learners improve their ability to prevent, detect, and respond. From syllabus to instructors, labs to learning. See this and similar jobs on glassdoor After completing this course, learners should be able to: You will learn proven mandiant. Te u is tr ib creative red teaming o n o t d participant guide / d mandiant. This table will display a list of all courses that are available from this provider. You will learn proven mandiant. Mandiant red teams have conducted hundreds of covert red team operations. This course draws on that knowledge to help learners improve their ability to prevent, detect, and respond to threats in an enterprise network. Dive deep into the world of. After completing this course, learners should be able to: Red team offensive security is an effective exercise for addressing security gaps. Mandiant red teams have conducted hundreds of covert red team operations. This course draws on that knowledge to help learners improve their ability to prevent, detect, and respond to. Te u is tr ib creative red teaming o n. It will also show the delivery method in which the course is given. However, organizations must still follow the right processes and use proven tools to enjoy all. This course includes apis and techniques used to perform common malicious functionality and extends these techniques to produce reliable payloads that function across operating system. Red team offensive security is an effective exercise for addressing security gaps. • identify, fingerprint and compromise a target with custom crafted payloads while bypassing antivirus (av) detection • deploy creative. Dive deep into the world of red teaming with our comprehensive review of mandiant's creative red teaming course. See this and similar jobs on glassdoor From syllabus to instructors, labs to learning. This table will display a list of all courses that are available from this provider. Mandiant red teams have conducted hundreds of covert red team operations. This course draws on that knowledge to help learners improve their ability to prevent, detect, and respond to. This course draws on that knowledge to help learners improve their ability to perform advanced offensive. Mandiant red teams have conducted hundreds of covert red team operations. This course draws on that knowledge to help learners improve their ability to prevent, detect, and respond to threats in an enterprise network. All courses can also be purchased using expertise on. Basically all the classic red team topics, opsec consideration, c2 infrastructure, phishing techniques and toolings, initial acccess vectors, lateral movements, persistence techniques.Mandiant Creative Red Teaming (2021) Download Free PDF Security
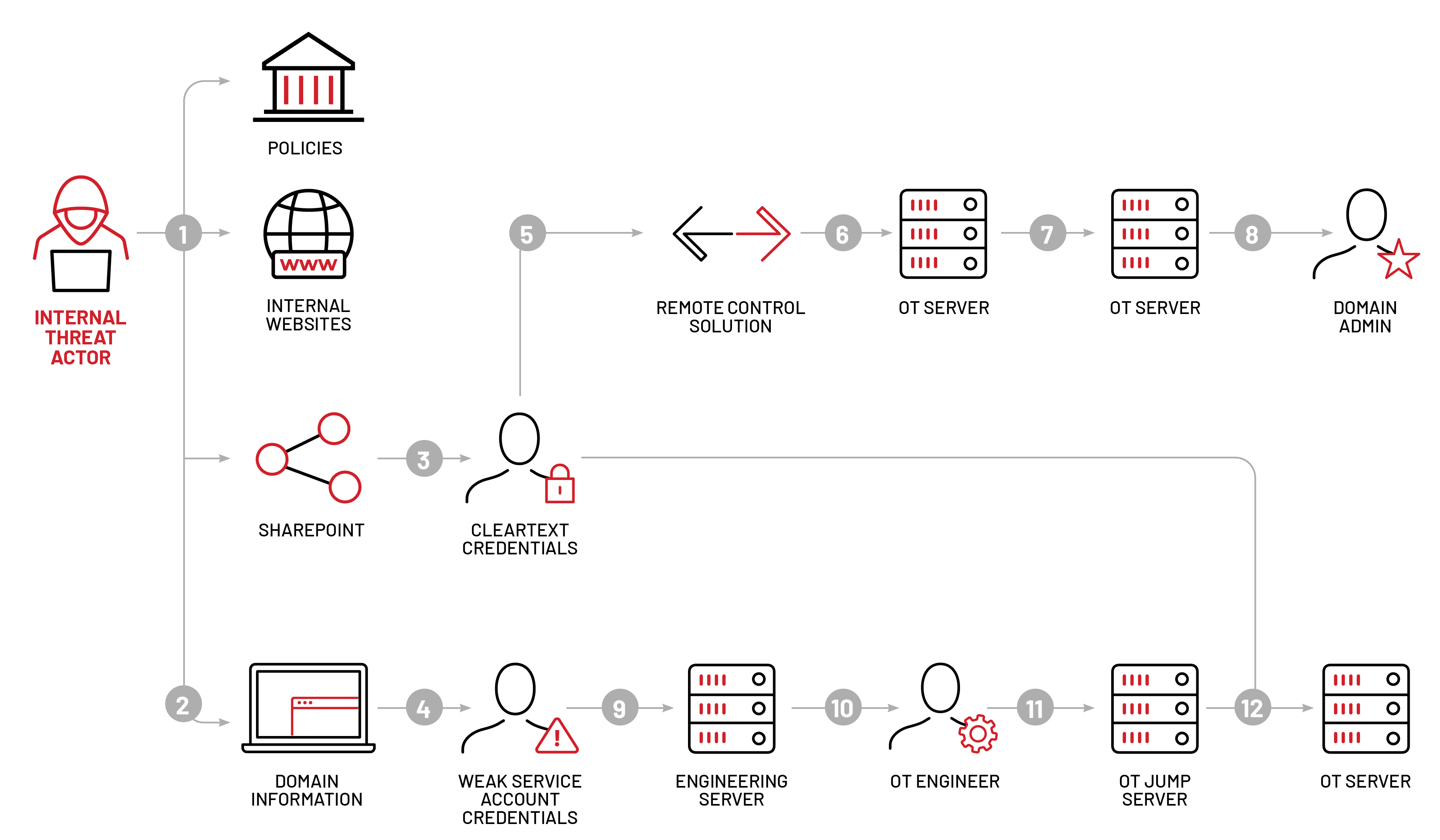
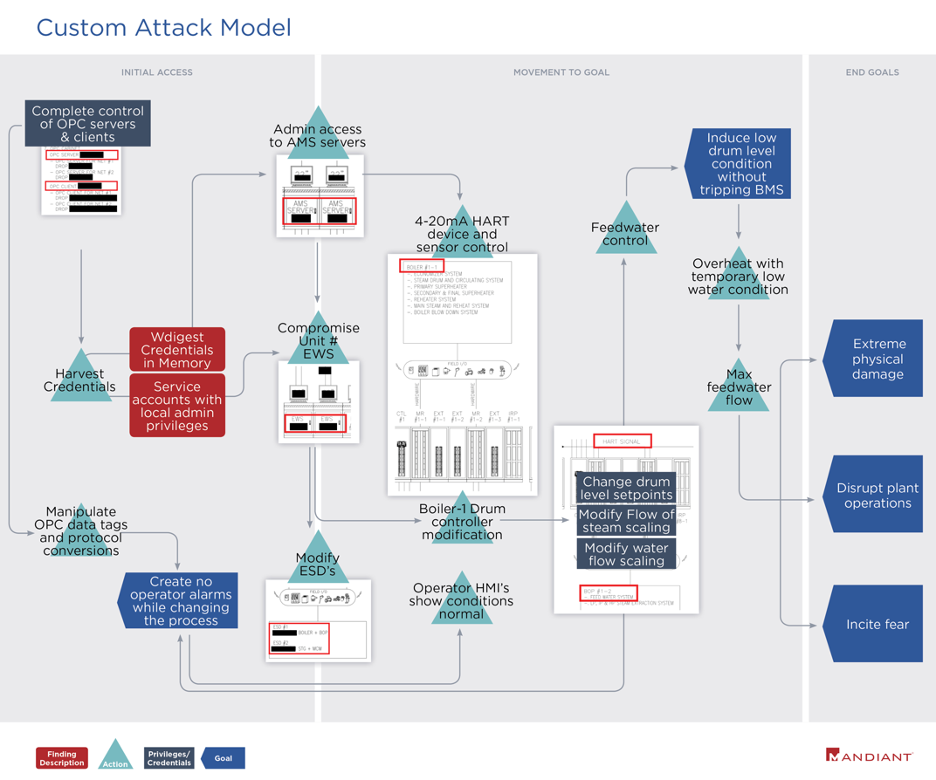
Mandiant Red Team Emulates FIN11 Tactics To Control Operational
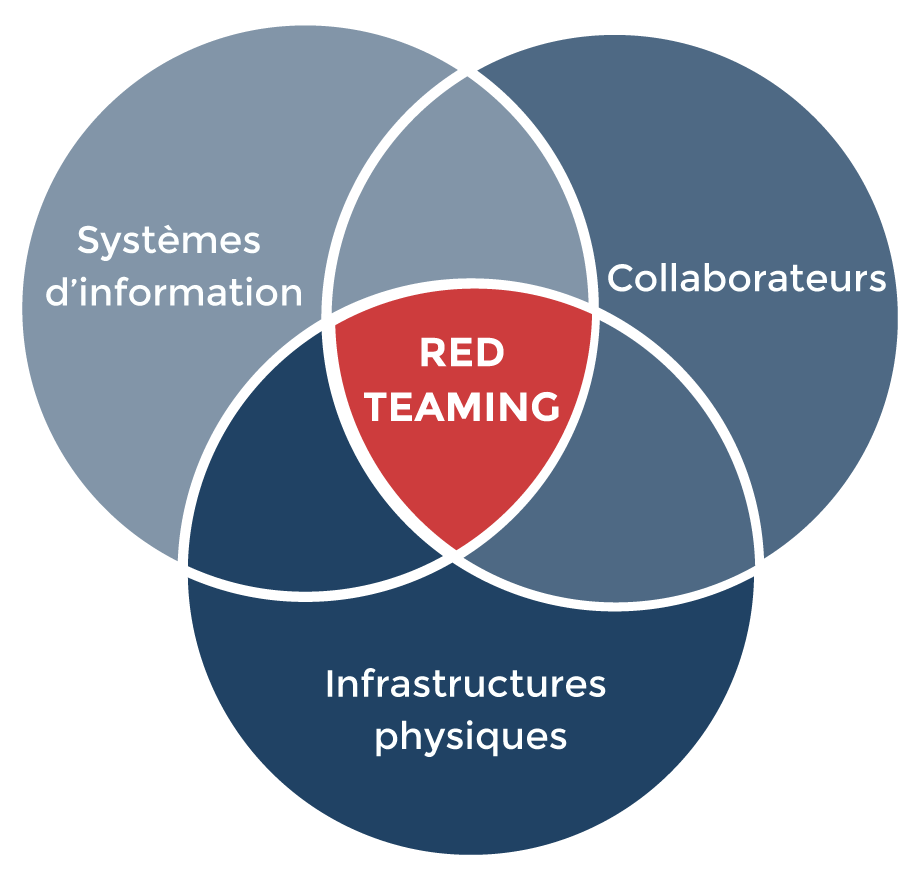
Qu'estce que le Red Teaming et comment
Red Teaming What It Is, Benefits, and How It Compares
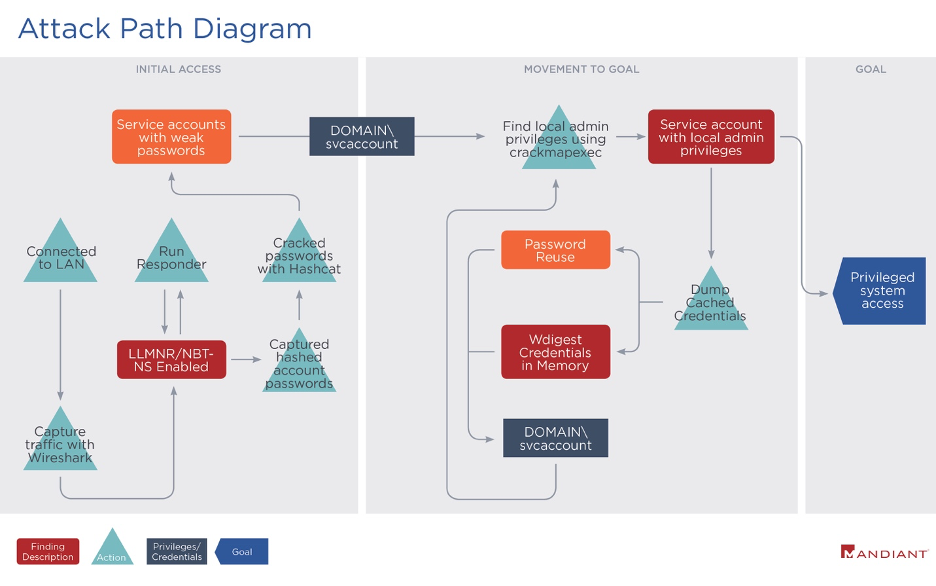
Mandiant Red Team Case Study Mandiant Red Team Case Study
OT Red Teaming Mandiant's Approach for OT Red Teaming Google Cloud Blog
Red Team Training Bundle
What Is Red Teaming? PlexTrac
OT Red Teaming Mandiant's Approach for OT Red Teaming Google Cloud Blog
Mandiants 'Creative' Red Team Review YouTube
Te U Is Tr Ib Creative Red Teaming O N O T D Participant Guide / D Mandiant.
After Completing This Course, Learners Should Be Able To:
By Applying To This Position…See This And Similar Jobs On Linkedin.
Mandiant Red Teams Have Conducted Hundreds Of Covert Red Team Operations.
Related Post: